

Just gonna leave this here.


Just gonna leave this here.


Yes, this is it. I bought it because it was cheap (100€) and had a built-in CPU. The only problems are that it hasn’t got many SATA or PCIe ports. This is fine however, because I have no need for them right now.



This is a custom built mini PC, with a mini-ITX motherboard and an Intel N100 CPU. It gets powered by a power supply that I got from an old computer. Also, it needs no active cooling, just a heatsink. It almost never gets above 60°C.
(and yes, it has no case).
In it I run:


Oh, I missed the L1 in the title. Basically, all the decryption at L1 is happening inside a Trusted Execution Environment. This is a dedicated chip that does all encryption-decryption (among other things). This is why it is so difficult to extract the keys, because they don’t enter the CPU or are stored in RAM, because the dedicated chip handles all of these.
So I don’t think you can find a guide about this, because if anyone has found even one exploit, they would be keeping it to ourselves, so that it doesn’t get patched.
Although it is very difficult, I think the only real solution is to reverse engineer a TEE and find an exploit yourself.
If you manage to do this, please let me know! I am happy to get updates about progress in this topic.


I have heard about a TamperMonkey userscript called EMELogger that logs some information about EME, in the web tools console making it easier to get the PSSH. I haven’t tried it though.
Also, I don’t think you will find guides on paid content as this is considered highly illegal (I think).
I managed to fix this problem by pointing my domain name to my private IP address (with pihole’s local DNS entries), so I could access it. Then, I just got certs for the domain and applied them with nginx.
I know, but for some reason my router does not let me access my domain (with duckdns) when connected to my network. So even if I get certs for the domain, I will not be able to access it. I have set up local DNS entries (with Pi-Hole) to point to my srrver, but I don’t know if it possible to get certs for that, since it is not a real domain.
EDIT: Fixed it. (See reply for fix)


So, OP has 45.57 gold medals only for his first torrent on the list?


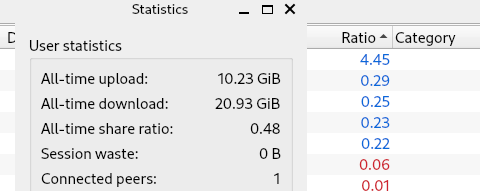
I am waiting for my medal


Yes, basically on internal LAN I put admin admin to everything.


I wish I could like a comment twice on Lemmy.
I just use ext4 on everything. It works pretty nicely.


I think you can encrypt drives by using a key stored in the TPM, if you have one. See the Arch wiki for info.
Though I have heard the TPM is not as secure..
I recently bought a motherboard with a N100 processor, that had two 3.0 USB Ports, two 3.1 USB Ports, an HDMI and a DisplayPort. Because of that I was surprised to learn that it had also two PS/2 ports for a keyboard and a mouse.


I’d rather not. :)




Yes, I have little bandwidth so I always download low bitrate ones.


I don’t have any job that needs to run 24/7, so I poweroff my server at night (12 am) and start it in the morning using WOL.


OK, maybe I will think about some other use for the Raspberry Pi then.
After having upgraded my Pi-Hole to v6, for some reason yesterday it started to not recognize any of the blocklists. So, I resetted it and now it works.